Let's Encrypt
Let's Encrypt is a certification authority (CA), that issues free domain validated X.509 certificates. Such certificates are the base for encrypted communication in the internet via HTTPS protocol. Let's Encrypt facilitates the certificate management of website operators. To this end, CA relies on a high degree of automation, to issue certificates to all owners of a domain for free and without complications. The Research Group of Lets´s Encrypt consists of members from Mozilla, Cisco and CoreOS.[1] Furthermore, there are more than 100 sponsors that support the project.
Terms
| term | meaning |
|---|---|
| digital certificate (Format X.509) | An identity proof that clearly identifies websites (server and domains). A user can clearly understand that he communicates with the desired server. |
| certification authority (CA) | The issuer of digital certificates. In addition, the CA certifies the certificate with its signature. Users can trust the certificate of the server (Chain of Trust). The only prerequisite is that the CA is trustworthy. |
| Cross-Signatures | The next link in the chain of trust for the user is the web browser. In order to establish a trustworthy HTTPS connection, a browser must trust the CA's signature on the DV certificate. Let's Encrypt has ensured that current browsers trust Let's Encrypt signatures via a cross-signature from IdenTrust.[2] |
| Domain Validation (DV) | If the owner of the example.com domain wants a digital certifcate for its domain, the CA must proof that he is the legitimated owner of example.com. This is implemented, for example, via a confirmation link sent to an email address belonging to the domain or via the mechanisms used by Let's Encrypt.Let's Encrypt issues currently only DV certificates. |
| Extended Validation (EV) | The EV expands the DV with a clearer identity verification of the certificate applicant. |
| Public and Private Key | Public or private keys are used for the verification and creation of certificate signatures. The most important cryptographic algorithm is RSA in this context. This can be verified directly in a X.509 certificate - Public Key Algorithm: rsaEncryption.[3]The private key is created when certificates are requested from the domain owner's server and is not passed on or transferred to the CA in any form. The safety of the Private Key is crucial for a safe communication via HTTPS. |
FAQs
The FAQs answer frequently asked questions:
- Frequently asked questions (letsencrypt.org)
The following blog post explains why the duration at Let´s Encrypt certificates is limited to 90 days:
- Why 90 Days (letsencrypt.org)
Automatized domain validation
Let's Encrypt issues automatized certificates - also on the CA side. The ACME protocol forms the basis for communication between domain owners and CAs:[4]
Automated Certificate Management Environment (ACME) is a protocol for automating the management of domain-validation certificates, based on a simple JSON-over-HTTPS interface.
Flowchart
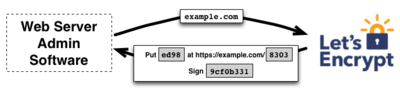
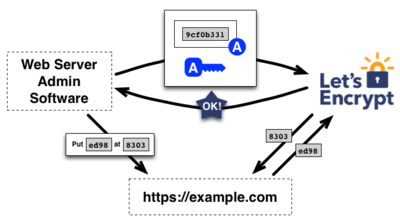
- The webserver demands a signed certificate. Let's Encrypt then gives him a task that he must complete. Possible tasks are for example a DNS recorder or set up a resource under the given domain.
- The webserver gets a Nonce (initialisation vector) in addition to its task that will get signed with the private key of the webserver (the key used to submit the request).
- If step 1 and 2 have been performed successfully, the CA issues a signed certificate.
Let's Encrypt client
The Let's Encrypt client is a python written command line tool.[5] The client takes over the communication with Let's Encrypt to:
- request certificates
- configure webservers for certificates
- renew certificates
- revoke certificates
Review
The Let's Encrypt client has also been criticized, since it handles root privileges (via sudo) extensively and currently only configures Apache and Nginx automatically.[6] As the ACME protocol is available for free, there are also alternative clients:
- List of Client Implementations (letsencrypt.org)
References
- ↑ Internet Security Research Group
- ↑ Let's Encrypt is Trusted (letsencrypt.org)
- ↑ X.509 (wikipedia.orf)
- ↑ ACME (wikipedia.org)
- ↑ Let's Encrypt at github
- ↑ The status of Let's Encrypt (blog.uberspace.de)
More information
- Certificates from Let's Encrypt in Apache, Nginx and HAProxy (www.admin-magazin.de)
Author: Georg Schönberger
 |
Translator: Alina Ranzinger Alina has been working at Thomas-Krenn.AG since 2024. After her training as multilingual business assistant, she got her job as assistant of the Product Management and is responsible for the translation of texts and for the organisation of the department.
|