SNMP basics
The Simple Network Management Protocol (SNMP) is a network protocol for supervising and controlling network devices such as routers, switches, firewalls, printers or NAS appliances. SNMP has been expanded step by step and supports an authentication as well as an encryption of transferred data in version SNMP v3. In this article, yu will find basic information on SNMP and the differences between SNMP versions.
Basic information
The SNMP protocol is located in the application layer of the OSI layer model.[1] [2]
Ports used
The connection is established without connection via UDP ports 161 and 162.[3]
- UDP 161 to query agents
- UDP 162 for traps, automatic notifications, are sent to managers in the event of abnormal agent behavior.[4]
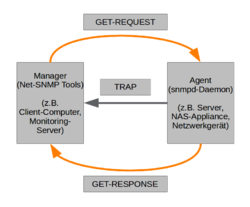
Agent
The agent component of SNMP typically runs on the monitored server system, appliance, or network device. You can record system states, configure settings, and also trigger actions. One of these agents is snmpd, which is a daemon that depicts agent components on Linux based operating systems.[5]
Manager
Only the second of both components is used on the client server or on monitoring server. Sie dient zur Abfrage der Daten, oder aber auch um Aktionen ausführen zu können. Meist ist jedoch nur eine eingeschränkte Konfiguration der Agenten auf vielen Appliances vorhanden, es können meist nur Daten abgefragt werden. Bei Linux-basierten Betriebssystemen bilden die Applikationen des NET-SNMP Paketes diese Manager-Rolle aus. Es kann bequem per apt installiert werden, siehe Abschnitt [SNMP einsetzen].
Generally, agents with the following data package can be administrated:
| data package | description | example tool |
|---|---|---|
| GET-REQUEST | used for requesting a specific data set and a clear OID must be stated | snmpget[6] |
| GETNEXT-REQUEST | runs through the following data sets, for example tables | snmpgetnext[7] |
| GETBULK | retrieve specified number of records at once, similar to multiple GETNEXT-REQUESTS | snmpwalk[8] |
| SET-REQUEST | changing one or multiple data sets | snmpset[9] |
| GET-RESPONSE | receives the answer on one of the pre-sent packages | snmpstatus[10] |
| TRAP | unforced message, when an event occurs, from the agent to a manager | snmptrapd[11], this daemon runs on the manager systems, for example monitoring servers and listens to port 162 UDP. |
SNMP versions
The following table compares the parameters of the three currently used SNMP versions that are required for SNMP Data Query with snmpget and snmpwalk. In the monitoring area, a Nagios plugin called “check_snmp” is primarily used. For example, our own TKmon service checks for Synology NAS are based on this plugin. Some of the parameters differ in this plugin. For example, the parameter -o is required before specifying the OID.
| SNMP v1 | SNMP v2c | SNMP v3 | |
|---|---|---|---|
| authentication | community-string | username, passwort | |
| encryption | - | pre-shared-key | |
SNMP v2
SNMP v2 existed in various forms. The form, that still exists, is v2c. The expansion c means community-based SNMP. It is SNMP v1 compliant in terms of security and has been enhanced with additional features from the obsolete v2p, party-based SNMP. Tables are therefore queried using GetBulk rather than GetNext, as it was the case in v2. It enables a communication between individual managers. Unlike the already discontinued versions v2p and v2u (user-based SNMP), version v2c has become established and enjoys the broadest support in the market.
SNMP v3
Security features were insufficient up to and including SNMP v2, which is why SNMP v3 was specified. It greatly increases security through features such as user names and passwords, as well as data transmission encryption. The complexity naturally increases at the same rate. There are more configuration methods available compared to v2c. The User Based Security Module (USM) is used, which is currently the only one supported by SNMP v3 [12] USM is defined in RFC 2574.[13]
Important hint: When the supervising network supports v3, v3 should definitely be preferred over v2. It should also be done with the highest possible level of security, for example, transmission encryption should not be omitted if it is supported. Devices from Synology only support, for example, the --AuthNoPriv method, which means that encrypted password authentication is used, but the data is transmitted in plain text.[14] [15]
The following table shows configuration options of SNMP v3 and the necessary parameters for querying with snmpwalk.
| kinds of authentication and encryption | description | required parameters for snmpwalk |
|---|---|---|
| noAuthNoPriv | no authentication, no transmission encryption of data, stating username | -l noAuthNoPriv -u <Username> |
| authNoPriv | authentication, no transmission encryption of data, request of username and password | -l authNoPriv -u <Username> -A <Passwort> -a <MD5|SHA> |
| authPriv | authentication and transmission encryption of data, requesting username, password and password of encryption | -l authPriv -u <Username> -A <Password> -a <MD5|SHA> -X <Pre-Shared-Key> -x <DES|AES> |
Insert SNMP
The SNMP function can be activated within less steps. The following examples show the configuration on a Synology NAS and Ubuntu.
Network-Appliances
With standard appliances, the SNMP function can usually be conveniently configured via a web interface. You will find the configuration at Synology NAS devices in the Control Panel under the "SNMP" tab of the "Terminal & SNMP" menu item.
Installation under Ubuntu
With Linux based operating systems like Ubuntu, the SNMP function can be conveniently retrofitted using package management.
Installation of agent
The agent is installed on the server to be monitored using apt:
sudo apt install snmpd
Installation of manager
Installing the tools on the manager side is just as easy, for example Linux notebook or monitoring server:
sudo apt install snmp
This package contains the snmpget and snmpwalk tools.
Example configuration of snmpd agent
Using the typical example of a network appliance, in this case a Synology NAS, we will now look at the configuration of an snmpd agent. Connect via SSH to the target host.
cat /etc/snmp/snmpd.conf rocommunity syno localhost rocommunity <plaintext password> //Reading access via Community-Passwort, access via SNMP v2c, password stored unencrypted rocommunity6 <Klartextpasswort> createuser thomas-krenn MD5 relation //v3-User rouser thomas-krenn //"rouser" means that only one reading access is allowed.
OIDs
The OIDs, Object Identifier, is the identifier for objects worldwide.[16] An OID represents a node in a hierarchical namespace. Each node is uniquely identified by a sequence of numbers. This means that the position of the node can be determined in the tree. The longer the chain, the more specific the information. Many nodes in the OID tree do not contain any information, but only references to the nodes below them. OIDs consist of integers and are concatenated using dot notation, for example. Other representation types include ASN.1 notation, as used in MIBs, and URN notation.
Example of OIDs
The following examples illustrate the structure of an OID.
- Top Node
- root of OID tree
- OID assignments from the top node
- Internet OID
- Internet Private Enterprises OIDs
- 1.3.6.1.4.1
- 1.3.6.1.4.1 - IANA-registered Private Enterprises
- Every company has a unique node below the Internet Private Enterprise node.
- Synology has, for example, number 6574. This results in the following combination: 1.3.6.1.4.1.6574
MIBs
In addition to OID chains, MIBs (Management Information Bases) are another central component of a network management protocol such as SNMP. The objects are called Managed Objects and are written in specification language ASN.1. THe MIBs contain no data, but provide explanations on where to find information and how they look, for example, what return values there are for the specific OID, or what data type is used.
Example entry of a MIB
Synology provides detailed information on the used OIDs and MIBs.[17] In this document, the used MIB files are linked. An exemplary excerpt of the MIB SYNOLOGY-RAID-MIB.txt shows the structure of an entry.
[...]
raidStatus OBJECT-TYPE
SYNTAX Integer32(1..12)
MAX-ACCESS read-only
STATUS current
DESCRIPTION
"Synology Raid status
Each meanings of status represented describe below.
Normal(1): The raid functions normally.
Degrade(11): Degrade happens when a tolerable failure of disk(s) occurs.
Crashed(12): Raid has crashed and just uses for read-only operation.
Note:
Other status will be showed when creating or deleting raids, including below status, Repairing(2), Migrating(3), Expanding(4), Deleting(5), Creating(6), RaidSyncing(7), RaidParityChecking(8), RaidAssembling(9) and Canceling(10).
"
::= { raidEntry 3 }
[...]
More information
- Object Identifier (OID) Repository (oid-info.com)
- Simple Network Management Protocol (de.wikipedia.org)
- Simple Network Management Protocol (en.wikipedia.org)
- SNMP - Simple Network Monitoring Protokoll (dietmueller.at)
- An Introduction to SNMP (Simple Network Management Protocol) (digitalocean.com)
References
- ↑ Application layer (corresponds to OSI-layer-5–7) (de.wikipedia.org)
- ↑ SNMP - Simple Network Management Protocol (elektronik-kompendium.de)
- ↑ 4. Protocol Specification (tools.ietf.org)
- ↑ Net-SNMP Tutorial -- traps (net-snmp.org)
- ↑ SNMPD.CONF (net-snmp.org)
- ↑ SNMPGET (net-snmp.org)
- ↑ SNMPGETNEXT (net-snmp.org)
- ↑ SNMPWALK (net-snmp.org)
- ↑ SNMPSET (net-snmp.org)
- ↑ SNMPSTATUS (net-snmp.org)
- ↑ SNMPTRAPD (net-snmp.org)
- ↑ [1] (net-snmp.org)
- ↑ User-based Security Model (USM) for version 3 of the Simple Network Management Protocol (SNMPv3) (ftp.ietf.org)
- ↑ Secure Your SNMP!! (penturalabs.wordpress.com)
- ↑ Security Comes to SNMP: The New SNMPv3 Proposed Internet Standards - The Internet Protocol Journal - Volume 1, No. 3 (cisco.com)
- ↑ Object Identifier (de.wikipedia.org)
- ↑ Synology DiskStation MIB Guide (global.synology.com)
 |
Author: Thomas Niedermeier Thomas Niedermeier working in the product management team at Thomas-Krenn, completed his bachelor's degree in business informatics at the Deggendorf University of Applied Sciences. Since 2013 Thomas is employed at Thomas-Krenn and takes care of OPNsense firewalls, the Thomas-Krenn-Wiki and firmware security updates.
|
 |
Translator: Alina Ranzinger Alina has been working at Thomas-Krenn.AG since 2024. After her training as multilingual business assistant, she got her job as assistant of the Product Management and is responsible for the translation of texts and for the organisation of the department.
|
