Update Intel Microcode under VMware
VMware regularly releases microcode updates for Intel CPUs for ESXi. After installing such updates, new Intel Microcode versions are installed during the starting process. In this article, we show how to verify the Microcode version on a server with VMware ESXi 6.7 and install newer microcode versions as needed.
Example of setup
In this example, we use the following setup:
- Server with ASUS P10S-M Mainboard with BIOS version 4401 (notification: This example is not on the VMware HCL)
- VMware ESXi 6.7 (directly after installation, for now, without applying any patches)
The test was conducted on August 27, 2018, using the latest available BIOS, microcode, and software versions at that time. This clearly demonstrates how the latest security updates—both microcode and software updates—can be applied in security-critical environments.
Read out BIOS version
First, verify the BIOS version:
[root@localhost:~] esxcfg-info | grep -i bios
|----BIOS UUID................................................0x50 0xaa 0xab 0xc 0x5d 0x93 0x17 0x2c 0x39 0x7b 0x2c 0x4d 0x54 0x47 0xd 0xc1
|----BIOS Vendor..............................................American Megatrends Inc.
|----BIOS Version.............................................4401
|----BIOS ReleaseDate.........................................2018-03-05T00:00:00
|----BIOS Asset Tag...........................................To Be Filled By O.E.M.
|----Name............................................HardwareSMBIOSHeap
|----Group Name..........................HardwareSMBIOS
|----World Command Line.................................grep -i bios
|----Option Name........................................ignoreHwSMBIOSInfo
[root@localhost:~]
If it is a Thomas-Krenn system, the latest BIOS version for the mainboard can be found in the BIOS security updates article. In this example, the latest BIOS-version available is already existing.
Read out current Microcode version
The currently available Microcode version can be read out on the SSH shell with the vsish command:
[root@localhost:~] vsish -e cat /hardware/cpu/cpuModelName Intel(R) Xeon(R) CPU E3-1220 v6 @ 3.00GHz [root@localhost:~] vsish -e cat /hardware/cpu/cpuList/0 | grep -i -E 'family|model|stepping|microcode|revision' Family:6 Model:158 Stepping:9 Number of microcode updates:0 Original Revision:0x00000084 Current Revision:0x00000084 [root@localhost:~]
In this example, the current Microcode version 0x84 is available.
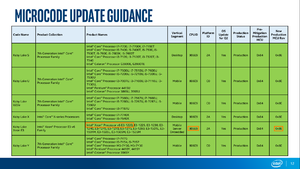
Intel provides information on available Microcode versions in the Microcode Update Guidance document (see Intel Microcode - Microcode versions). In this document, CPUs are listed by their CPUID (not by family/model/stepping). In the full output of the vsish cpuList command, the CPUID can be found in the "1:CPUID leaf" section under "EAX" (in this example, 0x906e9):
[root@localhost:~] vsish -e cat /hardware/cpu/cpuList/0
CPU information {
Family:6
Model:158
Type:0
Stepping:9
[...]
CPUID:CPUID content {
0:CPUID leaf {
EAX:0x00000016
EBX:0x756e6547
ECX:0x6c65746e
EDX:0x49656e69
}
1:CPUID leaf {
EAX:0x000906e9
[...]
Number of microcode updates:0
Original Revision:0x00000084
Current Revision:0x00000084
[...]
Alternatively, the CPUID can be determined in the following way based on Familiy/Model/Stepping:
- Note Family/Model/Stepping in Hex format. The /proc/cpuinfo file outputs the values in decimal format:
- Family: 6 -> 0x6
- Model: 158 -> 0x9e
- Stepping: 9 -> 0x9
- The CPUID has the setup 0FFM0FMS. Now work your way from the back to the front to determine the CPUID based on Family/Model/Stepping:
- S (Stepping) = 9
- M (last digit of the model number) before: e9
- F (Family) before = 6e9
- The digit 0 before = 06e9
- Model (penultimate digit of the model number) before that = 906e9
When searching for "906e9" in the "Microcode Update Guidance" document dated August 8, 2018, the "New Production MCU Rev" column lists microcode version "0x8E". In this case, Intel is providing a newer microcode version than the one currently installed on the system.
Install patch
VMware provides Microcode updates together with other patches for download.
Install all available updates (as described in the article Update VMware ESXi). In this example, the ESXi670-201808402-BG update is contained, which contains the new Microcode.[1]
Query microcode
Checking the microcode version after applying the patches and restarting the host shows the new microcode version 0x8E:
[root@localhost:~] vsish -e cat /hardware/cpu/cpuList/0 | grep -i -E 'family|model|stepping|microcode|revision' Family:6 Model:158 Stepping:9 Number of microcode updates:1 Original Revision:0x00000084 Current Revision:0x0000008e
References
- ↑ VMware ESXi 6.7, Patch Release ESXi670-201808402-BG - Updates cpu-microcode VIB (VMware aknowledge base article 56538)
More information
- Using the ESXi 6.0 CPU Microcode Loading Feature (blogs.vmware.com, 08.05.2015)
 |
Author: Werner Fischer Werner Fischer, working in the Knowledge Transfer team at Thomas-Krenn, completed his studies of Computer and Media Security at FH Hagenberg in Austria. He is a regular speaker at many conferences like LinuxTag, OSMC, OSDC, LinuxCon, and author for various IT magazines. In his spare time he enjoys playing the piano and training for a good result at the annual Linz marathon relay.
|
 |
Translator: Alina Ranzinger Alina has been working at Thomas-Krenn.AG since 2024. After her training as multilingual business assistant, she got her job as assistant of the Product Management and is responsible for the translation of texts and for the organisation of the department.
|
